
© Dmitry Demidovich/Shutterstock.com
Key Points
- Communication and trust are key to developing a culture centered around cybersecurity.
- Focus on the easy, small wins you can achieve daily. These count toward your overall posture.
- Build a culture that isn’t afraid to report incidents as they happen.
Integrating some regular Kaizen practices into your security department is a powerful foundation. Rather than relying on the likes of regular audits and penetration testing to see where vulnerabilities might lie, daily, incremental changes can lead to sustainable and lasting improvements.
Cybersecurity itself is taking the utmost precedence when looking at the state of businesses in 2025. The influx and mass adoption of data have made many organizations a sitting duck without a strong framework for addressing threats and remediating them.
While Kaizen is typically thought of as a solely Lean-centric practice, you can use that notion for continuous improvement to greatly enhance your cybersecurity posture. Today, we’re taking a look at some practical strategies you can execute daily to lead to a more secure organization.
Team Huddles and Communication

A conference room with a meeting taking place discussing quarterly results.
©Gorodenkoff/Shutterstock.com
One of the most crucial things you can do to enhance your cybersecurity posture is to simply communicate. You want to foster a culture of open, transparent communication. This doesn’t just build a rapport with your front-line employees and other personnel, but it also opens up avenues for quick and decisive problem-solving. When an incident happens, your team will know how to communicate, making for effective responses.
Visual management boards are a great tool to integrate for the sake of communication. You can display key metrics, show the real-time status of your cybersecurity posture, and look at the likes of active threats. As with communication, this helps to promote transparency and serves as a means of motivating and guiding the ship, as it were, for your team.
Gemba Walks
Taking a physical tour of your workplace can be a fantastic means of understanding how your team is handling cybersecurity on the whole. While Gemba walks are typically reserved for factory floors in Kaizen, they can be readily applied to security teams. Checking with your personnel daily can help apprise you of the current challenges being faced by staff. Further, it allows you to see the processes in how incidents and security as a whole are handled.
Daily Stand-ups
Before starting the work day, a brief team meeting can be held. This allows your team to discuss what has been done, what needs doing, and raise any pressing security issues or concerns. Stand-ups aren’t just for the sake of micro-management, but also keep communication open and free. With any luck, you’re fostering an environment where transparency can lead to quick and effective incident resolution.
Micro-Improvements and Problem-Solving
Rather than undertaking large, sweeping changes after an audit, focusing on the smaller improvements is going to yield far better results. You’ll likely want to focus on small wins or integrating a small improvement daily. These can be relatively simple tasks, like running a phishing simulation for employee training, mandating password changes, and so forth. However, the point of these small wins is to focus on making improvements daily. Making it a regular practice guarantees your team is building momentum and carving a path towards a better cybersecurity posture.
Root Cause Analysis
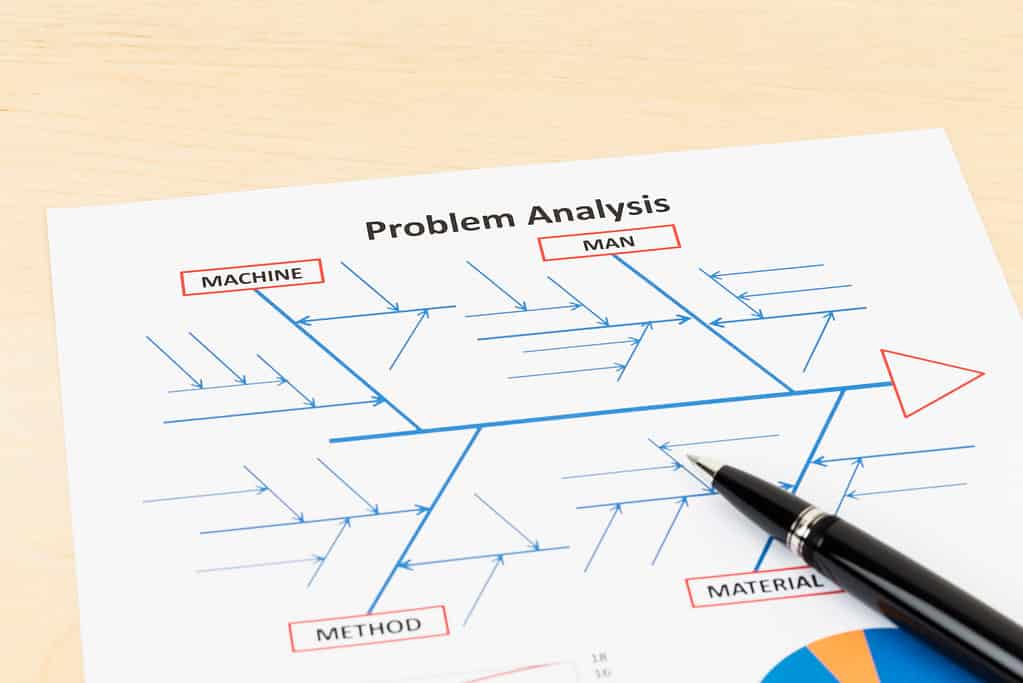
Often, when an incident occurs, we default to the SOP established by the department. Instead, also consider taking a look at the root cause of what caused the incident to occur in the first place. A system like the 5 Whys can hone in on areas of concern for your security team and allows for swift deployment of improvements. Consider the following scenario using this method:
Why did a user download a malicious attachment? They didn’t recognize it as a threat.
Why didn’t they recognize it? They lack security awareness training.
Why do they not have adequate training? Because the training schedule is sporadic, and is only conducted every year or so.
Why is the training schedule so sporadic? There isn’t a clear owner for the training program.
Why isn’t there a clear owner? There are no defined roles or responsibilities for cybersecurity personnel.
In this hypothetical scenario, you haven’t just determined the root of the problem, but you’ve also discovered where to address the problem going forward. While part of your team works to isolate and remediate the issue, a clearly defined process owner can move forward with drafting a more comprehensive and frequent method of employee training for security needs.
Standardization
When processes are improved, documentation is key. However, I’ll suggest that you go a step forward when considering documentation, and make standardizing these processes part of the SOP going forward. This guarantees consistency in incident response and creates a comprehensive overview of how to address problems for employees as they onboard. You aren’t just documenting successes, but drafting a blueprint for future processes with standardization.
Fostering a Security-Conscious Culture

Security isn’t solely the responsibility of your cybersecurity personnel. If you’re looking to build a stronger cybersecurity posture, you’ve got to get everyone involved in it. This means empowering all employees, regardless of their position or department. Your digital hygiene is only as effective as the weakest link in your organization, and providing adequate training goes a long way.
Further, you want to create an environment where there is no blame for incidents. Employees might not report incidents out of fear of punishment for a mistake. Instead, you want to create an environment where mistakes are acknowledged, and an appropriate response to remediate the incident is in place. Building a culture where an employee feels comfortable enough to report an incident that might be their fault is going to lead to a more secure organization on the whole.
Daily Security Reminders
A basic thing you can do is to send out a daily email with a security tip. These don’t have to be comprehensive overviews of security principles for the digital domain. Instead, it could just be something simple, like a reminder not to reuse passwords. These little pro-tips can be integrated into security messages that show on a workstation’s screensaver.
You can even deliver these reminders and tips at the end of meetings. You want security to be the primary focus, not something lingering in the background.
Regular Audits and Reviews
If you’ve been in cybersecurity for long enough, this goes without saying. For those fresh to the industry, regular audits are heavily recommended. More major audits can be saved for every 6 months to a year or so. However, small daily checks can be a great way of observing where deficiencies are in your organization.
This is as simple as checking logs, reviewing if new patches have been released, and making sure that devices are properly vetted and configured before being connected to the company network.
Technical Practices

©Juice Flair/Shutterstock.com
Finally, you’ll want to take a daily look at the nuts and bolts that keep your machines running. Regular inventory audits should be conducted, even if on a smaller scale. It’s hard to protect what you aren’t aware of, and unknown assets can present an enticing attack surface for bad actors. If you’re looking to enhance your cybersecurity posture, even daily partial audits can help you keep an eye on the hardware, software, and data that run your organization.
Patching
Threats arise from new attack vectors every day, and it’s your responsibility as security personnel to make sure you’re regularly applying patches. Now, this doesn’t have to be done during hours of operation. You’ll want to make this a daily habit. However, testing patches on isolated machines before deploying them to the wider network is recommended. This helps to close up vulnerabilities, especially as critical patches arrive down the pipeline.
Automation
Where you can, you’ll want to integrate automation. Human beings are sharp, creative workers, but manual security tasks can be extremely tedious. Automating the likes of vulnerability scanning, log analysis, and threat detection can be a vast help. This also helps to free your team up for more complex, strategic issues.
Other Useful Tools and Concepts
Looking to keep learning today? You might want to take a closer look at how you can enhance your call center service. The average consumer sort of grins and bears it when it comes to dealing with call centers. However, we’ve got a practical guide for enhancing the customer experience.
Additionally, you might want to take a closer look at how you can implement lasting continuous improvement initiatives to address evolving cyber threats. Cybersecurity is never a static practice. Taking the steps to get in the groove with regular, adaptable responses is going to be key as you navigate your security duties.
Conclusion
Cybersecurity is a vital practice for any organization. By implementing some of the practices espoused in Kaizen, you can make lasting changes with just minimal effort exerted daily. Doing so now is going to pave the way for a more secure and capable organization.